Registrasi

Number Of Traffic Anomalies
1.1 Total Attacks: 76833
- User Total Attacks: 76833

Definition: Total attacks indicate the overall amount of activity that is considered an attempted attack against a protected zone. The higher the number of attacks, the more vulnerable the security of the organization's network.
Daily average: During the September period, daily attacks experienced significant fluctuations, it can be seen in the graph that the range of attacks was in the range of 1000-4000 with an average of 2000-2500 attacks per day. The highest Attack peak is in numbers 4000 attacks.
Bullish Engulfing Pattern: The graph shows a relatively up and down activity, at the beginning of the month it was stable at 2000-2500, then there was a decrease to 1500 on 4 and 5 September. Entering the middle of the month, attacks increased significantly and reached a peak of about 4000 on September 16, then decreased back to the 2,000's range on 19 to 21 September. After that, the trend returned to rise consistently on September 22 to 26 with a record high of around 3,600 attacks on September 25. By the end of the month, the number of attacks had dropped dramatically to 1,000 in 28 September, then jumped back more than 3,500 on September 30.
Explanation: A significant surge in 16 September most likely caused by coordinated attack campaign activities, such as distribution malware mass or attack brute-force which is done automatically. A pattern of rapid increases followed by decreases in the following days indicates that the attack was intense but not sustained, possibly because it was detected and limited by the defense system. U.S. stocks fluctuate amid economic data as energy shares slide 28 September can indicate a pause in the attack or a change in tactics of the attacker, before finally returning a sharp increase in 30 September which could be associated with the start of a new wave of attacks.
1.2 Attack Events: 188

Definition: Attack Events an attack event that has gone through the analysis process and is categorized as a significant threat to network security systems. Not all attacks on Total Attacks happens to be classified as Attack Event. Only those attacks that show a real pattern, impact, or potential damage to the system will fall into this category.
Daily average: The number of daily Attack Events ranges from 0 to 50 incidents per day. At the beginning of the month is relatively low with an average of under 10 events per day. Overall, if calculated roughly, the daily average is in the range of 15-20 events.
Development Pattern: The beginning of the month was relatively stable below 10 events per day, then increased from mid-September and reached a peak of about 30 events in 17 September. Thereafter the attack remained high, with another surge on the 25 September 35 events) and the end of the month, 29-30 September, which broke through more than 40 events.
Explanation: A significant increase in the middle to the end of the month is likely related to large-scale automated attack campaigns. The sharp decline in 28 September can be an indication of a pause in the attack, before reappearing a massive surge in 29-30 September which indicates that the attacker's activity is intensifying.
1.3 Monitoring Anomali Trafik
| No | IP Server | IP Attacker | Attack Types | Attack Count |
| 1 | 156.59.15.250 | 10.60.230.122, 10.80.17.157, 10.60.224.103 | Application Vulnerability. | 9246 |
| 2 | 156.59.11.138 | 10.60.230.122, 10.60.224.103, 10.60.224.150 | Application Vulnerability. | 9123 |
| 3 | 5.45.101.64 | 10.20.32.10, 10.30.112.47, 10.60.41.200 | Application Vulnerability. | 112 |
The table above provides information about the 3 servers that received the most attacks during the month monitoring period September 2025. The Server with IP 156.59.15.250 is the server that received the highest Attack and there are 9246 recorded attacks that happened.
Top 5 Malware Detection

1. Hacktool.Linux.Gsnetcat.V0gt
Total Detection: 5
Description: Hacktool based GsNetcat yang berfungsi mirip netcat, digunakan penyerang untuk membuat reverse shell, tunneling, atau port forwarding. This tool is often used to maintain unauthorized remote access.
Threat Level: High
Recommendations: Isolation of detected hosts. Perform a check of active processes and network connections. Remove malicious binaries as well as check persistence mechanisms (cron, systemd). Replace credentials that may have leaked and update the security system.
2. Trojan.Linux.Getshell.V383
Total Detection: 4
Description: A Linux Trojan that provides a remote shell to attackers. This Malware allows the execution of system commands and can be used to download additional payloads. It generally enters through the exploitation of vulnerable web services or applications.
Threat Level: High)
Recommendations: Immediately isolate the host. Audit system and application logs to identify initial entry points. Hapus file trojan dan hilangkan persistence. Apply the latest security patches to the exploited services and restore from clean backups if necessary.
3. Trojan.Generic.Script.Save.ba60
Total Detection: 2
Description: Generic detection for malicious scripts (e.g. Bash, Python, or PHP) that behave as Trojans. These scripts can execute malicious commands, open remote access, or download additional malware.
Tingkat Ancaman: Sedang-Tinggi (Medium-High)
Recommendations: Identify the location and content of the script before deleting. If running via cron or a web service, disable it immediately. Block the domain / IP that the script uses. Perform thorough scanning and strengthen security controls on the server.
4. Hacktool.Linux.Gsnetcat.V38q
Total Detection: 2
Description: Other variants of GsNetcat which is used to establish a reverse shell connection and remote communication with the attacker. Has similar functionality to the v0gt variant.
Threat Level: High
Recommendations: Isolation of detected hosts. Perform forensic triage of processes, network connections, and associated binary files. Remove dangerous artifacts after evidence is collected. Apply system hardening and monitor network traffic to prevent reinfection.
5. Backdoor.Generic-JavaSave.162d6dc
Total Detection: 1
Description: This is a generic detection for backdoors written in the Java language, usually targeting Java application servers such as Apache Tomcat or JBoss. This Malware allows attackers to gain remote access and execute commands at the server operating system level.
Threat Level: High
Recommendations: Isolate infected application servers. Perform security audits on running Java applications to find and delete files backdoor (often in the format .jsp or .war). Make sure the application server and library The Java used is always updated.
Bruteforce Attackers
2.1 Bruteforce Attackers
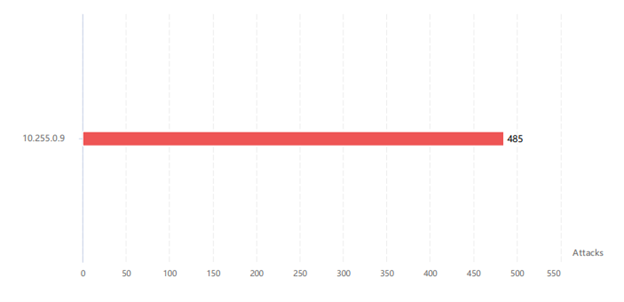
On bruteforce attack monitoring data throughout the month September, found one brute force attacker attack on the 13th endpoint. This makes it the only brute-force attack on the moon September, source brute-force attacks attacker derived from IP 10.255.0.9

From 13 endpoint attacked by IP 10.255.0.9, endpoint the most become top target, the attacker is endpoint 10.252.252.67attacked 70 times on the moon September here.
COMMON VULNERABILITIES AND EXPOSURES (CVE)
3.1 CVE-2025-10585
Google Chrome (Type Confusion) – Type Confusion / Potencial RCE
Skor CVSS: 8.8 (High)
Description: An incorrect data type vulnerability in Google Chrome's V8 JavaScript engine prior to version 140.0.7339.185 allowed a remote attacker to manipulate heap corruption through a specially designed HTML page. This issue is also relevant with Microsoft Edge, as it uses Chromium.
How It Works: Type-confusion in V8 engines makes JavaScript objects treated as wrong types resulting in heap corruption. This can be exploited via HTML/JS pages specifically designed to manipulate memory and ultimately allow arbitrary code execution (including possible sandbox escapes) on the browser process.
Impact: Successful exploits can lead to arbitrary code execution on affected systems, posing a significant security risk. Handling: apply the latest patches and updates provided by the relevant vendors.
Solution: Immediately update Google Chrome, Chromium, and Microsoft Edge to the latest versions that have been released by vendors to close these security gaps, temporarily restrict access to untrusted sites, and ensure that security systems such as EDR and SIEM are updated to monitor for potential exploits
3.2 CVE-2025-48543
Goggle Andorid – User-After-Free / Potencial RCE
Skor CVSS: 8.8 (High)
Description: Vulnerability use-after-free di Google Android yang memungkinkan sandbox escape dari Chrome untuk menyerang Android system_server.
How It Works: Penyerang dapat mengeksploitasi heap corruption melalui halaman HTML yang telah dimodifikasi, dan memanfaatkan type confusion dalam V8 JavaScript engine, Dapat dieksekusi secara remote melalui crafted HTML page.
Impact: Dapat menyebabkan arbitrary code execution pada sistem yang terpengaruh, kemudian risiko keamanan signifikan pada browser Chrome dan Edge, Exploit sudah ada di “in the wild” yang meningkatkan risiko serangan.
Solution: Update Google Chrome ke versi 140.0.7339.185 atau yang lebih baru, pastikan update Microsoft Edge ke versi terbaru, pastikan auto-update browser diaktifkan dan lakukan Monitor Google Chrome Releases untuk informasi patch terbaru.
3.3 CVE-2025-8088
WinRAR – A Path traversal
Skor CVSS: 8.4 (High)
Description: A path traversal path that affects the Windows version of WinRAR allows an attacker to run arbitrary code by creating a malicious archive file. This vulnerability has been exploited in the real world and was discovered by Anton Cherepanov, Peter Košinár, and Peter Strýček.
How It Works: Attackers create malicious archives containing files with special pathnames that can bypass WinRAR security validation. When the victim extracts the archive, WinRAR fails to properly validate the destination path, allowing the file to be extracted to a location it should not be on the victim's system.
Impact: This vulnerability has a very serious impact because it allows attackers to execute malicious code on the target system without the user's knowledge. Attackers can place malicious files into sensitive system folders, which can then be executed automatically or used to take over the system. Considering that WinRAR is a very popular application for managing archive files.
Solution: WinRAR users need to immediately update their application to the latest version that already fixes this vulnerability. In addition, users should apply the principle of caution when opening archive files from untrusted sources, and use antivirus software that is always updated. System administrators are also advised to implement policies that restrict user access rights to prevent the execution of malicious code, as well as conduct regular monitoring of suspicious activity on the system.
3.4 CVE-2025-49683
Windows Virtual Hard Disk )VHDX) – Eksekusi Kode
Skor CVSS: 7.8 (High)
Description: Kerentanan ini terjadi karena kesalahan penanganan bilangan bulat (integer overflow) pada komponen Virtual Hard Disk (VHDX) di Windows.
How It Works: Attackers who already have local access can create malicious VHDX files that, when mounted or processed by the system, trigger an integer overflow to run the code.
Impact: Attackers can execute code unlawfully on a victim's system, potentially compromising the integrity of the system.
Solution: Apply the latest patches and security updates for Windows provided by Microsoft.
3.5 CVE-2025-50154
WIndows File Explore – Information Disclosure
Skor CVSS: 7.5 (High)
Description: Receipt of sensitive information by unauthorized parties through Windows File Explorer allows unauthorized attackers to perform spoofing through the network.
How It Works: Attackers can take advantage of the exposed information to impersonate a legitimate entity on the network.
Impact: Potentially accessing resources that would otherwise be restricted, or carrying out more targeted social engineering attacks.
Solution: Microsoft has released a security patch that needs to be applied immediately to all affected systems. System administrators need to implement the latest Windows updates through Windows Update or WSUS for large organizations. As an additional measure, administrators are advised to apply the principle of least privilege, configure firewalls to restrict unnecessary network access, and conduct regular audits of folder sharing configurations to ensure no sensitive information is accidentally exposed to the network.
Cyber Security Hot News
4.1 Eksploitasi Zero-Day via File Gambar di Windows dan Aple (CVE-2025-53766 & CVE-2025-43300)
In September 2025, several critical vulnerabilities were recorded that had a significant impact on the security of network systems and enterprise applications, with three of them becoming a major concern for the cybersecurity world. CVE-2025-20333 the Cisco Secure Firewall allows remote code execution on edge devices, which if exploited can give attackers complete control over network traffic and internal systems. CVE-2025-53766 on Windows GDI + components allow attacks through malicious image files such as WMF or EMF, where malicious code can be executed by simply displaying or processing those images without user interaction. In the meantime, CVE-2025-54236 in Adobe Commerce opens up the potential for session takeover and code execution on public e-commerce platforms, putting them at risk for customer data leaks and operational disruptions. These three vulnerabilities indicate an increasing trend of exploitation of commonly used system components, confirming the importance of implementing security patches, network segmentation, and active monitoring of suspicious activity.
a. How The Attack Works
1. RCE via Input Terbuka / Deserialisasi
The attacker sends a structured payload (eg. malicious data deserialization or manipulated parameters) that make the application execute arbitrary code on the target server. Contoh: deserialization RCE di layanan enterprise
2. File-based Exploits (Gambar/Media)
File gambar yang dimodifikasi (WMF/EMF atau format lain) diproses oleh library OS (GDI+, ImageIO). Parsing bug (heap overflow / out-of-bounds write) menyebabkan corruption memori → kontrol aliran eksekusi → RCE.
3. Network/Protocol Attack (edge devices)
Weaknesses in the network stack (SNMP, ASA/FTD management interface) allow attackers to send packets/payloads that trigger buffer overflows or conditions that allow code execution or DoS.
4. Privilege Escalation / Local Exploit
LPE vulnerability (eg. Android ART, Windows NTLM / SMB) are exploited after basic access is gained or used for privilege escalation by malware.
b. Mitigation
1. Immediate patches-apply vendor-authorized security updates to all affected systems, especially Cisco ASA/FTD, Adobe Commerce / ColdFusion, and Microsoft.
2. Perimeter hardening-restrict access to management interfaces (use ACL or VPN-only) and enable WAF to block malicious payloads as well as high-risk files such as WMF/EMF.
3. Segmentation & least privilege-separate networks by function and apply the principle of minimal access rights to important accounts and services.
4. Monitoring & detection-enable EDR/IDS / IPS and monitor authentication logs, configurations, and suspicious network activity.
5. User awareness & endpoint protection-educate users not to open suspicious attachments and make sure the device is up to date and EDR/anti-exploit protected.
6. Fallback / emergency – if a patch isn't already available, reduce exposure by disabling vulnerable features, limiting file uploads, or isolating services until the update takes effect.
c. References :
• IConnect IT: IConnect IT: https://www.iconnectitbs.com/top-cyber-security-vulnerabilities-september-2025-roundup/
Cyber Contact Center
For cybersecurity incident reports or further support requests, please contact our security team at the following contacts:
- WhatsApp Only: 082319949941
- Website: servicedesk.telkomuniversity.ac.id (Info Kontak)
- Aplikasi e-Ticket PUTI: satu.telkomuniversity.ac.id (Ticketing)

